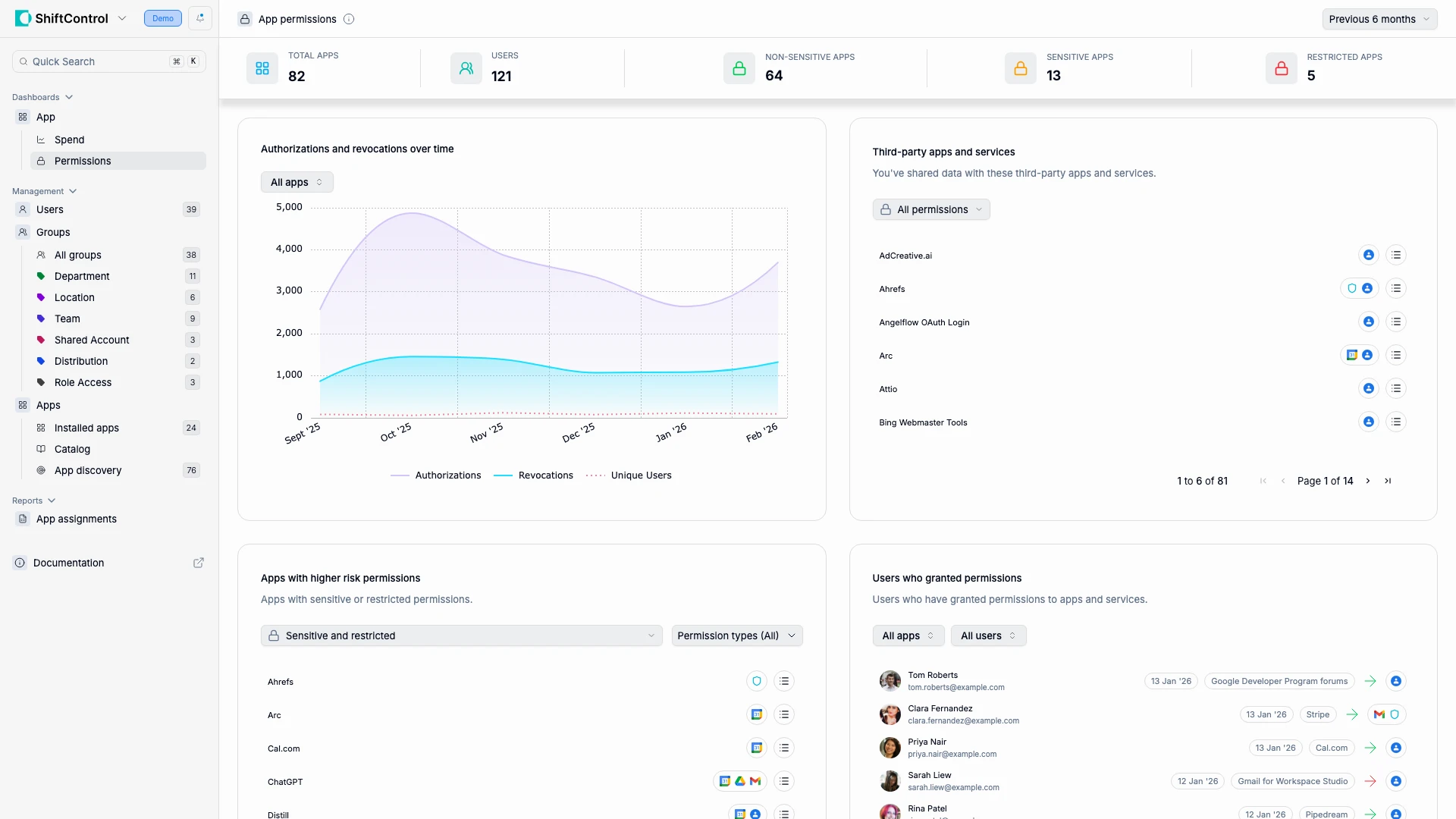
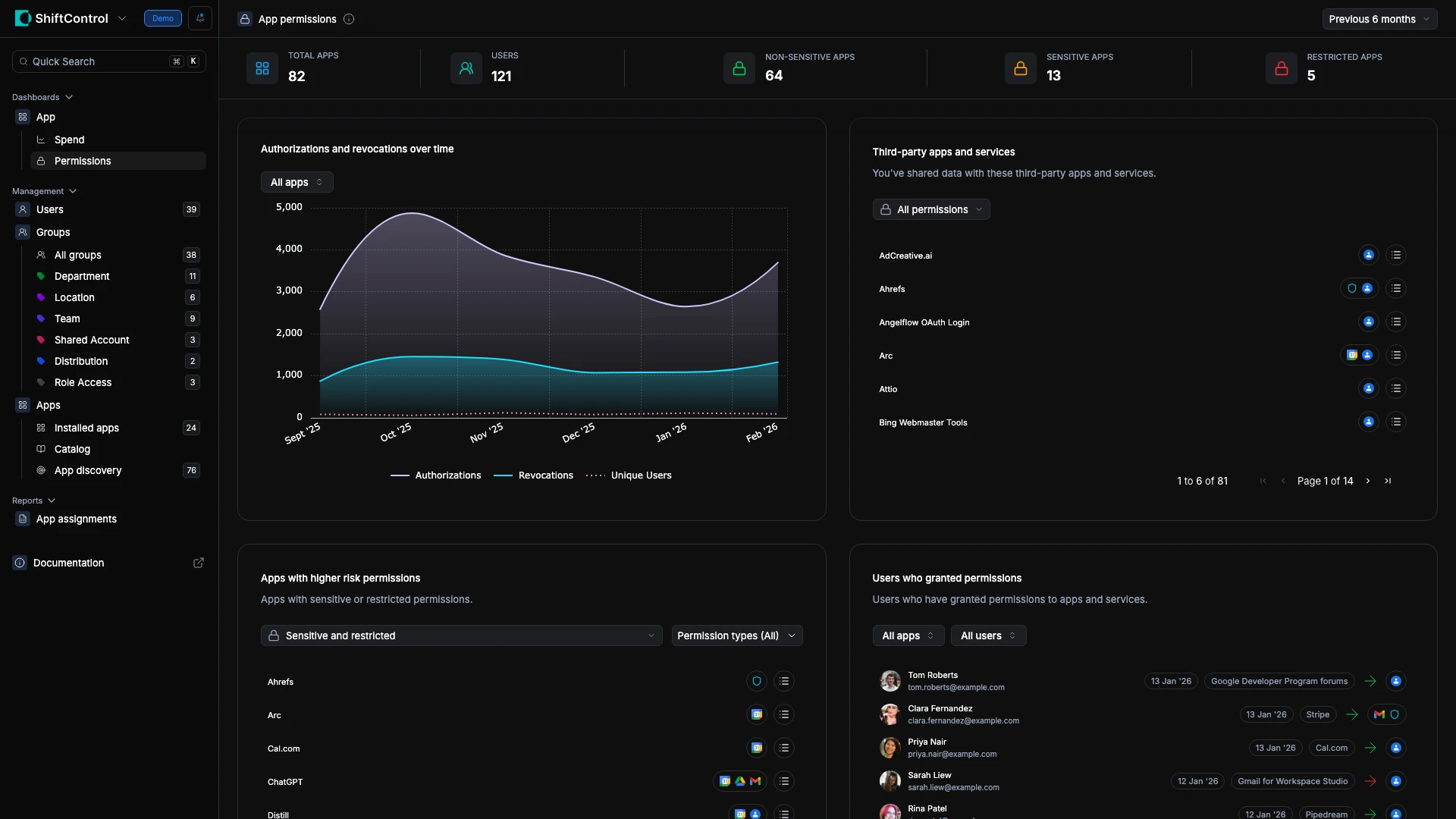
App Permissions Dashboard
See every third-party app your team has authorized, what data it can access, and who granted the permission — then take action.
Overview
Every time an employee clicks "Sign in with Google" or authorizes a third-party app, they're granting that app access to your organization's data. Most authorizations are harmless — a project management tool reading a user's profile. But some grant access to email, shared drives, or directory data, and those permissions persist until someone explicitly revokes them.
The App Permissions Dashboard makes this invisible web of access visible. Instead of discovering risky integrations during a security incident, you can monitor and manage them proactively.
How It Works
ShiftControl pulls OAuth authorization data from Google Workspace and aggregates it into four views:
Header metrics give you the big picture:
| Metric | What It Tells You |
|---|---|
| Total Apps | Distinct third-party apps authorized across your org |
| Total Authorizations | Active authorization grants (one app can be authorized by many users) |
| Unique Users | How many people have authorized at least one third-party app |
| At Risk Users | Users who authorized apps with sensitive or restricted permissions |
Use the date filter (top-right) to switch between Year to date, Last 90 days, or All time.
Common Scenarios
Scenario: Quarterly security audit
Your security team runs a quarterly review. Open this dashboard, filter to the last 90 days, and review "Apps with Higher Risk Permissions." You find a marketing tool with email read access authorized by three users. You click into one of those users to check their full App Permissions tab, decide the tool isn't approved, and revoke its access directly from the user's profile.
Scenario: Employee offboarding
When someone leaves, you need to ensure their third-party authorizations are cleaned up. Search for the departing user in "Users Who Granted Permissions" to see every app they authorized. Then click into their user profile and go to the App Permissions tab where you can review and revoke each grant individually.
Scenario: Investigating a suspicious authorization spike
The trend chart shows an unusual spike in new authorizations last Tuesday. You filter the Third-Party Apps list to that date range and discover a team rolled out a new integration without IT approval. You assess its permission scopes and decide whether to allow or revoke it.
Authorizations and Revocations Over Time
The trend chart tracks Authorizations (new grants) and Revocations (removed grants) over time:
- Steady growth in authorizations — your organization's shadow IT surface is expanding
- Authorization spikes — a team rolled out a new tool, or a batch onboarding happened
- Revocation spikes — a security review, offboarding event, or policy enforcement action
Watching both lines together tells you whether third-party access is being actively managed or growing unchecked.
Third-Party Apps and Services
Every app that users have connected through their Google accounts appears here. Filter by:
- Permission level — all, sensitive only, or restricted only
- Permission type — focus on specific data access categories
This is your master inventory. When someone asks "what apps have access to our data?" — this is the answer.
Apps with Higher Risk Permissions
Filters specifically to apps with sensitive or restricted permissions — apps that can read email, access shared drives, sync contacts, or modify data on behalf of your users.
For each flagged app, ask:
- Is it approved for business use? If not, revoke it.
- Who authorized it? One person using a niche tool is different from half the org.
- Are the permissions proportional? An app that needs calendar access but also requests email read permissions deserves scrutiny.
Apps with email, file access, or directory data permissions represent the highest data exposure risk. Review these every security audit cycle.
Users Who Granted Permissions
This panel shifts the view from apps to people — showing which users have the most third-party app connections.
Key workflows from this view:
- Click a user's name to open their full profile in User Management. From there, go to the App Permissions tab to see every active OAuth grant with details about what each app can access.
- Revoke permissions directly from a user's App Permissions tab — no need to open the Google Admin Console.
- Spot power authorizers — users with an unusually high number of app connections may be a security risk.
Things to Know
- Requires Google Workspace. This dashboard pulls data from Google OAuth logs. Without Google Workspace connected, there's no data to display.
- "At Risk" is based on permission scope. A user is flagged if they authorized any app with sensitive or restricted permissions, regardless of whether IT approved the app.
- You can revoke from ShiftControl. Click through to a user's App Permissions tab to revoke individual app grants without opening the Google Admin Console.
- Historical grants are included. An app authorized six months ago that was never revoked still appears in the totals.
- New apps classify quickly. Freshly authorized apps appear immediately; risk classification updates as ShiftControl processes the permission scopes.
Related Features
- Editing a User — App Permissions tab — View and revoke individual OAuth grants per user
- App Spend Dashboard — Monitor the cost side alongside permission risks
- App Discovery — Find unmanaged apps across your organization