User Management
Your single view of every person in your organization — who they are, what they can access, and whether their security is in order.
Overview
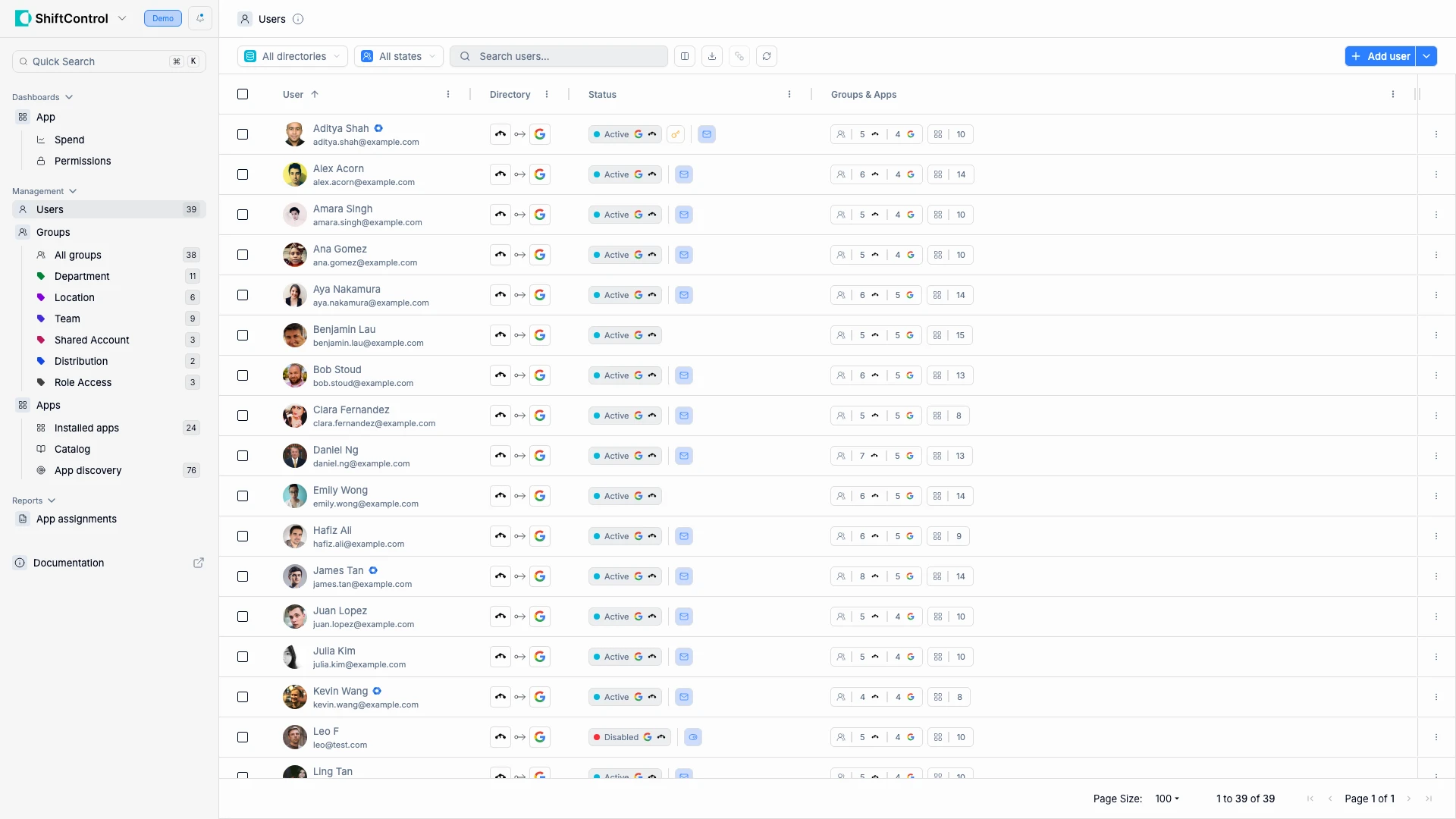
The Users page is the heart of ShiftControl. Every person in your organization has a row here, and that row tells you everything you need to know at a glance: their identity, which directories they belong to, whether they're active, and how many groups and apps they touch.
When you make changes here, they ripple through your entire stack. Activate a user and they get access to every app their groups provide. Deactivate them and access is revoked everywhere. Change their department and their group memberships — and therefore their app access — update automatically.
What You See
Each row in the users table shows:
| Column | What It Tells You |
|---|---|
| User | Name, email, and avatar — this is the identity used across all connected systems |
| Directory | Icons showing which directories the user exists in |
| Status | Active (can authenticate) or Inactive (access suspended) |
| Groups & Apps | How many groups they belong to and how many apps they can access |
Use the filters to narrow down what you're looking at:
- Directory filter — Show users from a specific directory only
- Status filter — Active, Inactive, or all
- Search — Find users by name, email, or other attributes
Common Scenarios
Auditing access before a compliance review
Your security team needs a list of everyone with active access. Filter to Active users, then review the Groups and Apps counts. Users with unusually high app counts warrant a closer look — click into them to see their full permissions. You can export this data for your compliance documentation.
Finding inactive users who still have app access
Filter by Inactive status. If any inactive user still shows a non-zero Apps count, their deprovisioning didn't complete fully. Click in to investigate and revoke remaining access. This is a common finding during security audits.
Bulk onboarding a new team
Your company acquired a five-person design team. Add each user and assign them to the Design group — their app access (Figma, Slack, Google Workspace) provisions automatically based on group membership. No need to configure apps one at a time.
User Actions
Click the ⋮ menu on any user row for quick actions.
Actions are context-sensitive — only actions that apply to the user's current status and your permissions are shown. For example, you won't see "Suspend" on an already-suspended user, or "Delete" if you don't have delete permissions.
Bulk Actions
Select multiple users with the checkboxes, then choose an action from the bulk menu. This is how you handle operations at scale — seasonal onboarding, department-wide password resets, or end-of-contract offboarding.
Each action is only enabled when at least one selected user is eligible. For example, "Activate" is disabled if all selected users are already active.
Things to Know
- Changes take effect immediately. Activating, deactivating, or disabling a user pushes the change to your connected directories in real time. From there, it cascades to every connected application.
- Deactivation vs. disabling. Deactivating suspends access but preserves the account and its data. Disabling is more aggressive — use it when someone needs to be locked out immediately and you don't need to preserve their state.
- Scheduled actions aren't instant. A scheduled deactivation means the user keeps full access until that date. Double-check the date if timing is critical for security.
- Pagination. The list shows 10 users per page. The total count (e.g., "1 to 10 of 36 users") is always visible at the bottom.
Related Features
- Adding a User — Create a new identity and start the onboarding process
- Editing a User — Update details, review security, audit permissions, track costs
- Groups — Manage the groups that control what apps users can access